Navigating cyber security in an open source world
This article was inspired by a talk at Future Rewired 2023.
The internet is a major part of everyday life and with it comes the need to ensure that data is kept secure. Cyber security is an important factor in protecting users from cyber criminals, hackers, and malicious actors. With the rise of open-source websites, there are even more opportunities for attackers to gain access to sensitive information. It is essential that businesses take steps to protect their networks and data from these threats by implementing robust cybersecurity measures.
At Future Rewired Joh Harvey Founder of the Raw Store, and Bruce McDougall and James Martel from Black Arrow Cyber Consulting ran a workshop for attendees covering key considerations for those building websites, and web applications.
At the event, Joh shared his story of the data breach that occurred to his business, and how using a popular website platform with added plugins to take orders online meant that there were holes in his website’s security. This was exploited and sensitive customer data was accessed by unauthorised users.


Open-source websites offer numerous benefits such as cost savings, flexibility, and ease of use; however, they also present unique risks due to their open nature. Since anyone can view the code behind an open-source website or application, this makes it easier for hackers to find vulnerabilities which they can exploit in order to gain access to confidential information or disrupt operations. This was the case in Joh's experience.
Joh found out about the breach when contacted by the police, and immediately contacted the ODPA to notify them of the breach. Following guidance from the ODPA, Joh contacted all of his customers to notify them of the breach, with further emails to customers who may have been at risk of theft of card details. Joh highlighted the importance of a rapid and honest response in maintaining trust, and protecting customers from further harm: "If I hadn't gone through these steps quickly because I was embarrassed, I might not have a business anymore. I'm lucky my customers sympathised with my situation and appreciated the quick reaction to the breach."
A true nightmare for any business owner. Joh expressed the need for website developers and the businesses that use them to take cyber security more seriously, and hoped that sharing his story would help to promote further transparency around breach events and highlight the risks to businesses.
Navigating cyber security in an open-source world requires vigilance and strong protocols in order to keep your data safe from malicious actors. The first step is understanding the risks associated with using such software. Since anyone can access the code, any weaknesses or vulnerabilities present may be exploited by hackers seeking to gain access to sensitive information or systems for nefarious purposes. Additionally, since there may not be a “centralised” control over who has accessed the code, keeping track of changes made can prove difficult if someone does manage to break into your system unnoticed.
Once you understand what risks could potentially arise from using open-source software, you must create measures designed specifically for addressing these issues within your organisation. This includes creating strict policies regarding password requirements as well as monitoring user activity on a regular basis so that any suspicious activity can be identified quickly and dealt with appropriately before further damage is done. It’s also important that all staff members are trained on how best to identify potential threats so they know when something should not be trusted or used without proper verification first.
During the hands-on workshop at Future Rewired, James took attendees through different scenarios of well-known data breaches using SQL injection and various software supply chain breaches. These were commonly down to easily patchable problems that could've prevented possible attacks. Bruce commented, "It's so important to maintain software and hardware, keeping your infrastructure up to date is critical!"
Staying up-to-date on patches and updates released by developers is largely the business's responsibility, these updates often contain fixes that address newly discovered vulnerabilities which could otherwise leave your systems exposed if left unaddressed. In addition, having multiple layers of defence (such as firewalls) will help prevent unauthorised access from occurring while ensuring that any attempts made are blocked before reaching critical areas of your network infrastructure.
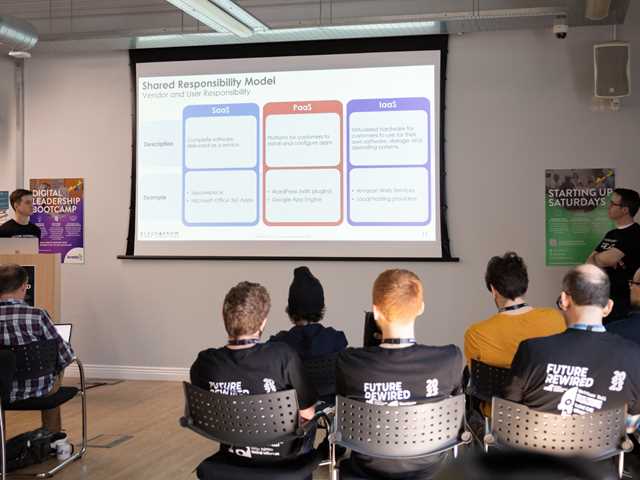
"It is the role of the business owner to know where the responsibility lies between the provider and the user of these open source resources."
James Martel, Black Arrow Cyber
Black Arrow Cyber's honey pot receives millions of attacks upon it a month, as bot-powered trawler software is constantly attacking online platforms and once it finds a fault, will alert a human handler and thus begins the 'cyber attack.'
Utilizing tools such as automated scanning solutions to monitor networks 24/7 will allow you to catch intruders early on – making them invaluable assets when dealing with cyber attacks aimed at targeting those leveraging open-source applications. Even though these types of programs require investments both financially and time-wise upfront, they ultimately pay off down the line since they provide additional protection even after other methods have failed due to their constant surveillance capabilities.
Overall, while there are always inherent risks involved whenever we use openly available sources, and taking steps towards mitigating them will go far towards helping secure your business against malicious intent looking to exploit its weaknesses - allowing you to maintain better peace of mind! The security conversation needs to be a constant thread throughout your business's development stage and onwards into usage and maintenance, deciding how to balance your priorities around usability, functionality and security.


